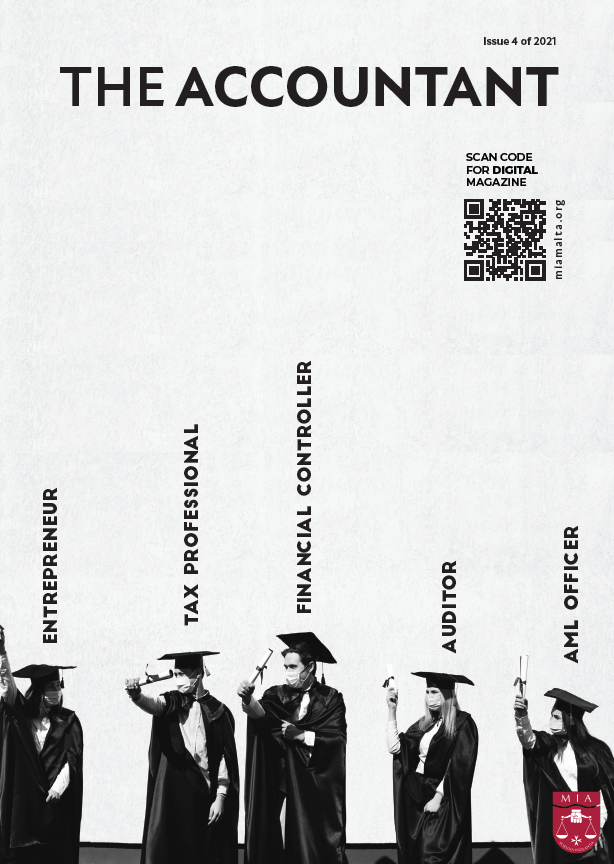
THE ACCOUNTANT |
The Accountant is the definitive guide for Accountants and Auditors, containing articles that are of interest to professionals working in public practice, and in the different Maltese industry segments such financial services, manufacturing and hospitality amongst others. Legal and financial consultants, judiciaries and trustees will also find The Accountant of interest.
The Accountant has established a reputation as being the foremost publication for the Maltese Accountancy and Audit profession providing a holistic approach covering unique financial and business related services and information to various sectors, giving a diversified insight into business processes, including (but not limited to) Auditing and Assurance, Accountancy, Tax, Regulatory and Compliance, Advisory and Corporate services.
Published quarterly, the Accountant delivers the editorial content to satisfy the market’s need to disseminate information fast and provide robust answers to the contemporary and emerging policy questions.
Ready to make the switch?
Members who do not wish to receive a physical copy of The Accountant delivered to them can follow the below steps.
We encourage everyone to utilise the digital versions provided below, as it contributes to our efforts to reduce paper usage. Furthermore, the digital version offers more accessibility and portability, and can be accessed before the postal service delivers physical copies.
Follow these steps to opt out of receiving physical copies of The Accountant:
- Log in and navigate to 'View Profile', then click ‘Edit Profile’.
- Find the ‘Consent and Preferences’ section.
- Find ‘The Accountant Publication Preference’.
- Select the option ‘I do not wish to receive a hard copy of The Accountant’.
LATEST EDITIONS
2024
2023
2022